What is a Web Application Firewall (WAF)?
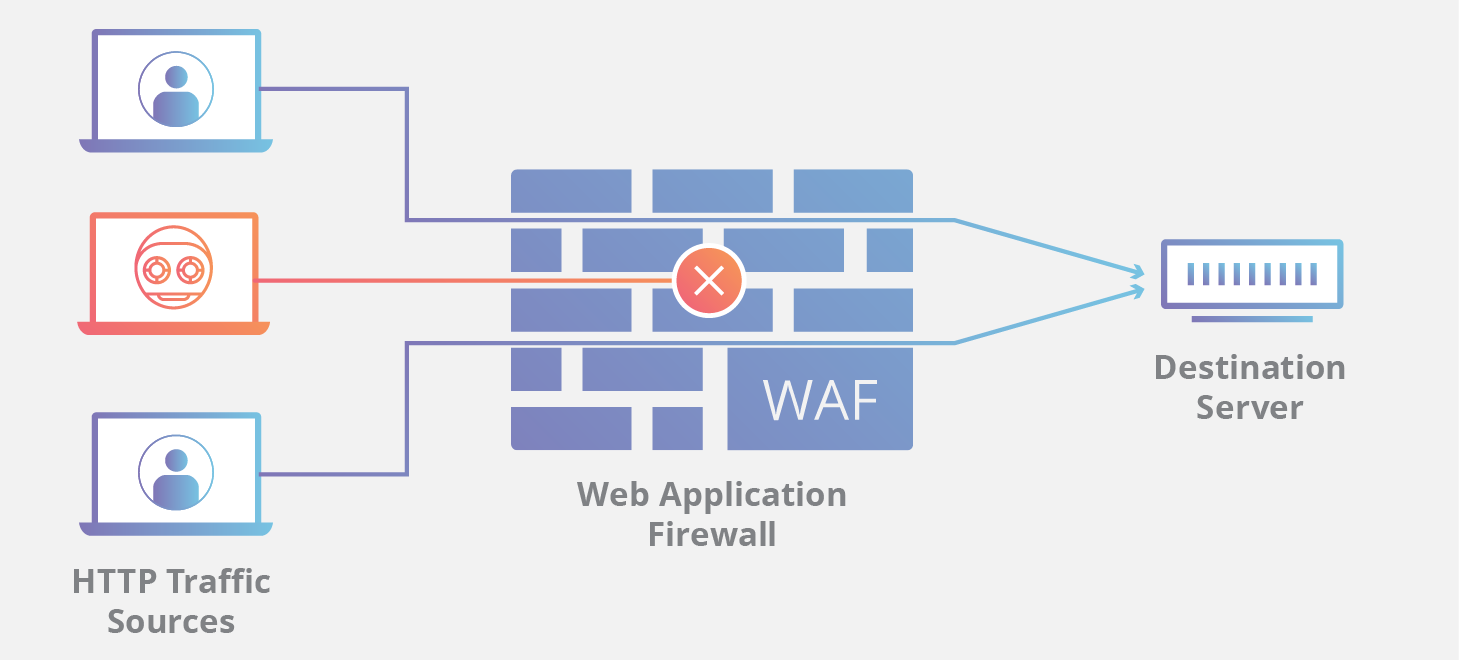
A WAF or web application firewall helps protect web applications by filtering and monitoring HTTP traffic between a web application and the Internet. It typically protects web applications from attacks such as cross-site forgery, cross-site-scripting (XSS), file inclusion, and SQL injection, among others.
A WAF is a protocol layer 7 defense (in the OSI model), and is not designed to defend against all types of attacks. This method of attack mitigation is usually part of a suite of tools which together create a holistic defense against a range of attack vectors.
By deploying a WAF in front of a web application, a shield is placed between the web application and the Internet. While a proxy server protects a client machine’s identity by using an intermediary, a WAF is a type of reverse-proxy, protecting the server from exposure by having clients pass through the WAF before reaching the server.
A WAF operates through a set of rules often called policies. These policies aim to protect against vulnerabilities in the application by filtering out malicious traffic. The value of a WAF comes in part from the speed and ease with which policy modification can be implemented, allowing for faster response to varying attack vectors; during a DDoS attack, rate limiting can be quickly implemented by modifying WAF policies.
What is the difference between blocklist and allowlist WAFs?
A WAF that operates based on a blocklist (negative security model) protects against known attacks. Think of a blocklist WAF as a club bouncer instructed to deny admittance to guests who don’t meet the dress code. Conversely, a WAF based on an allowlist (positive security model) only admits traffic that has been pre-approved. This is like the bouncer at an exclusive party, he or she only admits people who are on the list. Both blocklists and allowlists have their advantages and drawbacks, which is why many WAFs offer a hybrid security model, which implements both.
What are network-based, host-based, and cloud-based WAFs?
A WAF can be implemented one of three different ways, each with its own benefits and shortcomings:
A network-based WAF is generally hardware-based. Since they are installed locally they minimize latency, but network-based WAFs are the most expensive option and also require the storage and maintenance of physical equipment.
A host-based WAF may be fully integrated into an application’s software. This solution is less expensive than a network-based WAF and offers more customizability. The downside of a host-based WAF is the consumption of local server resources, implementation complexity, and maintenance costs. These components typically require engineering time, and may be costly.
- Cloud-based WAFs offer an affordable option that is very easy to implement; they usually offer a turnkey installation that is as simple as a change in DNS to redirect traffic. Cloud-based WAFs also have a minimal upfront cost, as users pay monthly or annually for security as a service. Cloud-based WAFs can also offer a solution that is consistently updated to protect against the newest threats without any additional work or cost on the user’s end. The drawback of a cloud-based WAF is that users hand over the responsibility to a third party, therefore some features of the WAF may be a black box to them. (A cloud-based WAF is one type of cloud firewall; learn more about cloud firewalls.)
Learn how a connectivity cloud lets companies protect their websites with a cloud-based WAF solution.
FAQs
What is a web application firewall (WAF)?
A WAF helps protect web applications by filtering and monitoring HTTP traffic between an application and the Internet. It defends the application layer, protecting servers from common threats like SQL injection, cross-site scripting (XSS), and cross-site forgery.
How does a WAF protect web applications?
By deploying a WAF, a shield is placed between the application and the Internet. Unlike a standard proxy that protects a client, a WAF is a reverse-proxy that protects the server by requiring all clients to pass through it before reaching the application.
What are the differences between blocklist and allowlist WAF models?
A blocklist (negative security model) denies traffic based on known attack patterns. In contrast, an allowlist (positive security model) only admits pre-approved traffic. Many WAFs use a hybrid of these models.
How can WAF policies be used during an active attack?
WAFs operate through sets of rules called policies that filter out malicious traffic. Because these policies can be modified quickly and easily, they allow for a fast response to new attack vectors, such as implementing rate limiting during a DDoS attack or blocking a new vulnerability exploit.
What are the three primary ways to implement a WAF?
WAFs can be implemented in the following ways: Network-based WAF: Typically hardware-based and installed locally to minimize latency. Host-based WAF: Integrated into the application software, offering more customization but consuming local server resources. Cloud-based WAF: An affordable and easy-to-implement security as a service option that provides consistent updates against new threats with minimal upfront cost.
Why might a company choose a cloud-based WAF over other options?
Cloud-based WAFs are often preferred because they offer turnkey installation and require no additional work or cost for protection against the latest threats. This process can often be as simple as a DNS change. While cloud-based WAF customers hand over some responsibility to a third party, they benefit from a solution that is updated to block new attacks without any effort on their end.